In this article I am going to show you how to attach a debugger and a VisualVM profiler to the Java application running on OpenShift. The approach described here doesn’t make use of the Jolokia bridge. Instead, we are going to leverage the port-forwarding feature of OpenShift.
The whole setup can be divided into three steps:
- Enable debug and JMX ports on the JVM
- Set up port forwarding
- Attach debugger and VisualVM to the forwarded ports
I am going to use OpenShift v3.11 that I installed using Minishift and a test application built with Java OpenJDK 1.8. This is how the complete setup is going to look like:

Hello world application
For those of you who want to follow along, let’s set up a test application which we will use for debugging. If you already have your Java application running on OpenShift, you can jump ahead to the next section.
Let’s deploy a Hello world application that I found on GitHub. This application was originally created to demonstrate how to build Vert.x-based microservices on OpenShift. You can get this application up and running in just two steps.
First, issue this command to build an S2I builder image for Vert.x applications:
| |
OpenShift started the build of the builder image and you can follow the progress with:
| |
At the end of the build process OpenShift pushed the new image into the integrated Docker registry. Next, we are going to use the builder image to build and run a sample Vert.x application:
| |
You can follow the build logs by issuing the command:
| |
If everything went fine, you should be able to see the Hello world application running:
| |
Enabling Debug and JMX ports on JVM
In the following, I am going to use OpenJDK 1.8. Note that the available JVM options may vary depending on the version of Java platform you are using.
To enable a remote debug port on JVM, one has to pass the following option to the JVM:
| |
In order to enable JMX, the following JVM options are needed:
| |
This set of options deserves a bit more explanation. By default, JMX utilizes RMI as the underlying technology for the communication between the JMX client and the remote JVM. And as a matter of fact, there are two RMI ports needed for this communication:
- RMI registry port
- RMI server port
At the beginning, the client connects to the RMI registry on port 3000 and looks up the connection to the RMI server. After the successful lookup, the client initiates a second connection to the RMI server. Based on our configuration, the client is going to connect to 127.0.0.1:3001. However, there’s no RMI server running on the local machine, so what’s the deal? As you will see in the next section, we are going to forward the local port 3001 back to the remote server.
Next, we need to convey our configuration options to the JVM running inside the OpenShift pod. It turns out that there exists an environment variable JAVA_TOOL_OPTIONS that is interpreted directly by the JVM and where you can put your JVM configuration options. I recommend using this variable as there is a great chance that this variable will work no matter how deep in your wrapper scripts you are launching the JVM. Go ahead and modify the DeploymentConfig or Pod descriptor of your application in OpenShift to add the JAVA_TOOL_OPTIONS variable. For example, you can open the DeloymentConfig for editing like this:
| |
… and add the JAVA_TOOL_OPTIONS environment variable to the container section of the specification:
| |
After applying the above changes, OpenShift will redeploy the application pod. At startup, JVM will print out the following line to the stderr which will show up in the container logs:
| |
This verifies that our JVM options are in effect and the debug port and JMX ports are open. How are we going to connect to these ports? Let’s set up port forwarding on the local machine next.
Setting up port forwarding
OpenShift features port forwarding that allows you to connect to an arbitrary port of a pod running on OpenShift. Port forwarding doesn’t require you to define any additional objects like Service or Route to enable it. What you need though is to start a port forwarding proxy on your local machine. Issue the following command on your local machine to start the proxy and forward the three ports 8000, 3000, and 3001 to the remote pod running on OpenShift:
| |
In the above command, remember to replace <POD> with the name of your application pod. If everything worked well, you should see the following output :
| |
Note that the proxy keeps running on the foreground.
Attaching to the JVM running on OpenShift
Having our port-forwarding proxy all set, let’s fire up a debugger and attach it to our application. Note that we instruct the debugger to connect to the localhost on port 8000. This port is in turn forwarded to the port 8000 on the JVM:
| |
After the debugger attaches, you can list existing JVM threads using the threads command:
| |
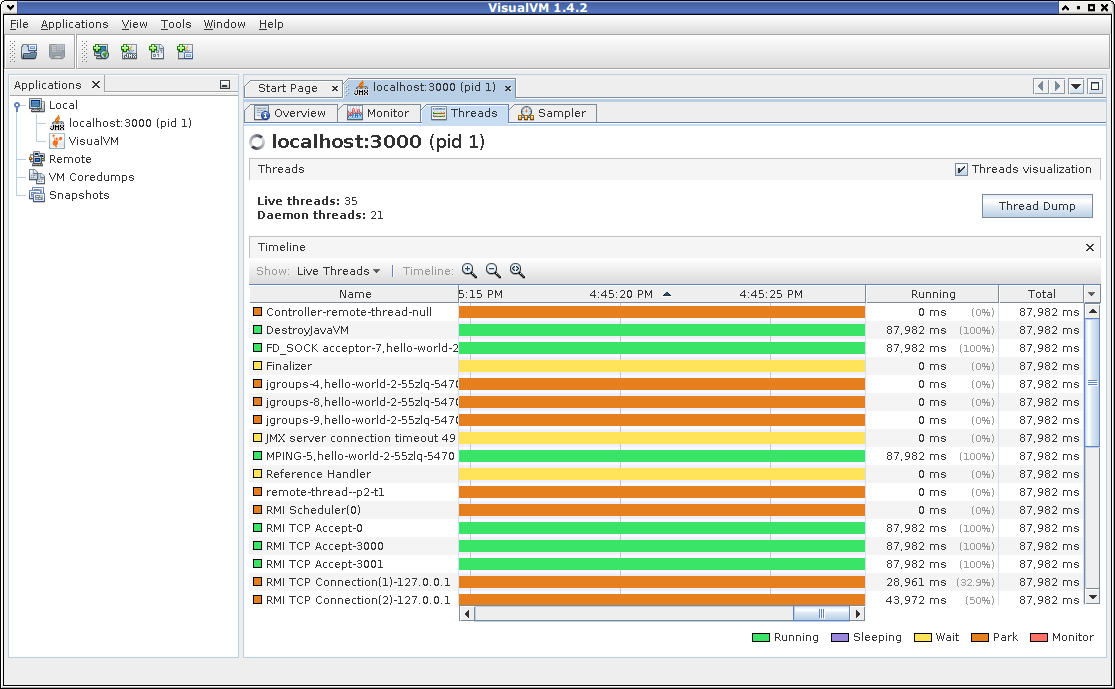
Next, let’s check out if we can attach VisualVM to our application as well:
| |
Works like a charm, doesn’t it?
Conclusion
In this blog post, we were able to attach a debugger and VisualVM to the Java application running on OpenShift. We didn’t need to deploy Jolokia proxy or create additional Service or Route objects to make our setup work. Instead, we leveraged the port-forwarding feature already available in OpenShift. The demonstrated method has additional security benefits as we are not exposing any additional ports of the application container.
Hope you enjoyed this article and was able to reproduce this setup for yourself. If you have any thoughts or questions feel free to add them to the comment section below.